Whether it’s on active or retired technology, your data is always on the line. The consequences of a data breach are too critical to overlook. Avoid being the center of yet another data breach headline by choosing a premium ITAD provider that is highly experienced, certified and reputable.
EPC goes to great lengths to ensure your data is protected. Every step of our process is certified and performed by highly-skilled professionals. You can rest assured knowing that your data is safe and secure with EPC.
Certified Processes
Our NAID AAA certified process follows NIST 800-88 standards and requires us to adhere to strict security policies at all times, helping you stay compliant with all local and federal regulations, including GDPR:
-
All facilities around the world have restricted access 24/7.
-
A thorough, documented chain-of-custody process is maintained for all sensitive materials.
-
All employees are subject to stringent background checks.
On-Site Data Destruction
EPC’s fleet of Data Destruction and Recycling Vehicles (DDRV) are compact, self-contained and engineered to efficiently shred all data-containing devices at your facility. While on-site, our experienced professionals will uninstall all hard drives, record serial numbers and shred devices individually. The entire process is captured on video, and you are invited to witness the process live. Once all drives are shredded, Certificates of Destruction are available online. We will then ship all equipment to one of our facilities for processing, remarketing and recycling.

SSD Data Destruction
Solid State Drives (SSDs) have become the preferred standard for data storage. SSDs are much faster and less vulnerable than traditional hard disk drives (HDDs). But the same qualities that make them superior are also challenges during the data destruction process. SSDs do not always respond to typical data erasure methods that use overwrites, magnets or shredders.
EPC’s SSD sanitization process includes a multi-phase, proprietary approach, using all available security protocols supported by SSDs. Additionally, we have custom-built shredders designed to turn SSDs into the legal minimum particle size, essentially turning your data into dust.
Both of these options can be performed at your facility so your data never leaves your custody.

Data Sanitization
By sanitizing hard drives and keeping them intact, you are likely to recoup a higher return on your original IT investment. EPC uses a variety of industry-standard data erasure software, allowing us to sustainably sanitize data across a wide array of IT. By erasing and reusing assets instead of physically destroying them, you can improve your security posture and address corporate social responsibility (CSR) requirements, while also ensuring compliance with local and global data privacy laws.
Our data sanitization solution can be performed by our trained technicians in several ways:

On-Site
Our technicians will sanitize every hard drive before it leaves your building. Then, we will properly pack and drive it to our closest facility for further processing, remarketing and recycling.

At EPC
You can choose to have EPC properly pack and drive your assets to our closest facility, or pack yourself and ship using your preferred carrier. Either way, once they reach EPC, your IT assets will be properly sanitized, processed, and remarketed or recycled. It’s important to note that choosing to have EPC pick up your assets transfers all potential transportation risks, including theft and damages, to EPC.
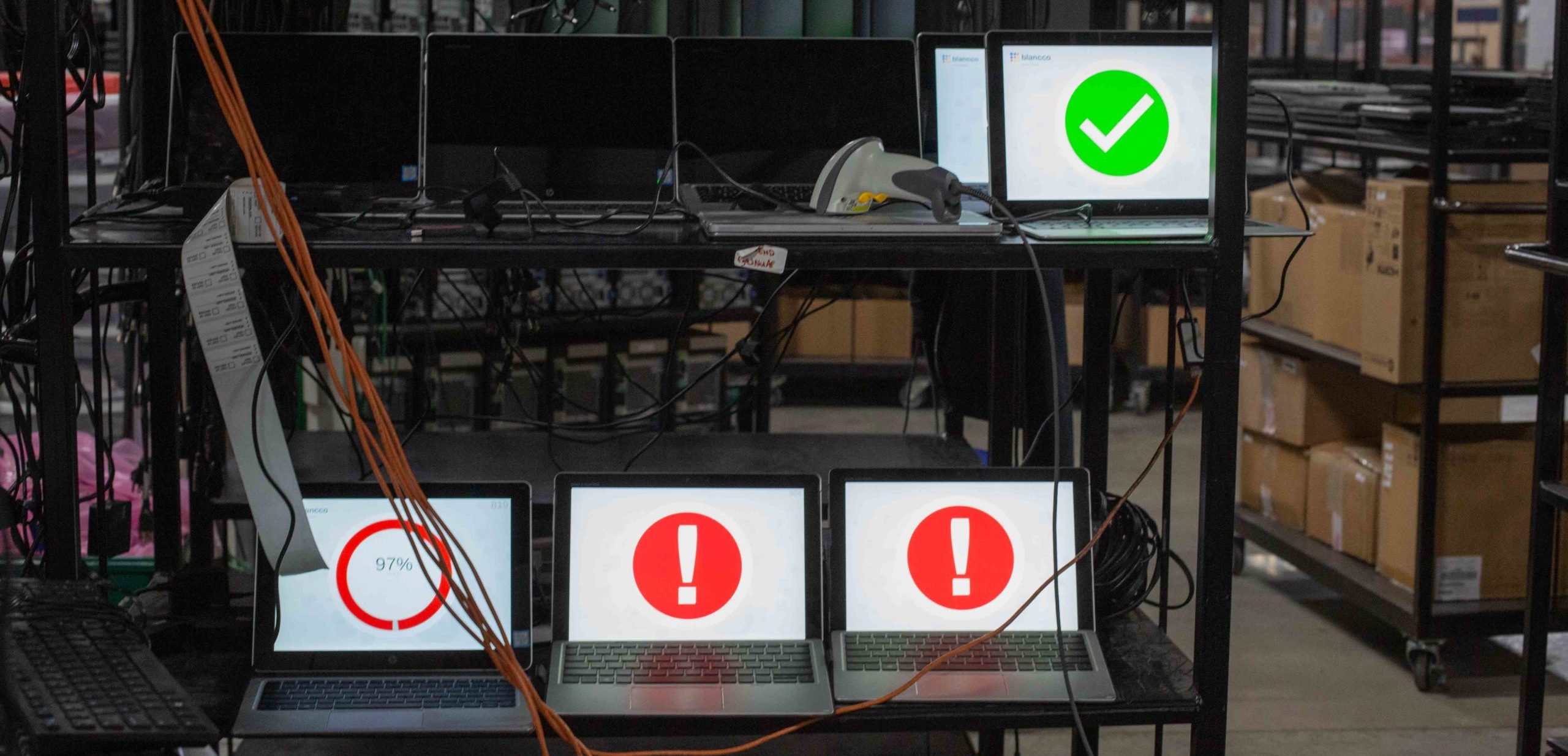
Remote Data Wipe
With our Blancco Remote solution, we can pre-install or remotely install Blancco on desktops, laptops and Windows tablets, allowing you to enable the software when it’s time to uninstall the asset. This provides easy, dependable, on-site data sanitization at your convenience for a minimal charge per license. It’s the ideal solution for organizations with hundreds, if not thousands, of low volume or single-item locations or remote users.
Let’s Connect
We tailor each and every ITAD project to reflect the customer’s security protocol. Contact us to build the solution that’s right for you.
